Title: Persistent XSS in Media File Renamer V1.7.0 Date: 1/31/2014Author: Larry W. Cashdollar, @_larry0Vendor: Notified 2/4/2014CVE: 2014-2040Download: http://www.meow.fr/media-file-renamer/Vulnerability:
In file mfrh_class.settings-api.php:
166 function callback_multicheck( $args ) {
167 $value = $this->get_option( $args['id'], $args['section'], $args['std'] );
168
169 $html = '';
170 foreach ( $args['options'] as $key => $label ) {
171 $checked = isset( $value[$key] ) ? $value[$key] : '0';
172 $html .= sprintf( ' %3$s %s', $args['desc'] );
176
177 echo $html;
178 }
function callback_radio( $args ) {
186
187 $value = $this->get_option( $args['id'], $args['section'], $args['std'] );
188
189 $html = '';
190 foreach ( $args['options'] as $key => $label ) {
191 $html .= sprintf( ' %3$s %s', $args['desc'] );
195
196 echo $html;
197 }
function callback_wysiwyg( $args ) {
250
251 $value = wpautop( $this->get_option( $args['id'], $args['section'], $args['std'] ) );
252 $size = isset( $args['size'] ) && !is_null( $args['size'] ) ? $args['size'] : '500px';
253
254 echo '';
255
256 wp_editor( $value, $args['section'] . '[' . $args['id'] . ']', array( 'teeny' => true, 'textarea_rows' => 10 ) );
257
258 echo '
';
259
260 echo sprintf( ' %s ', $args['desc'] );
261 }
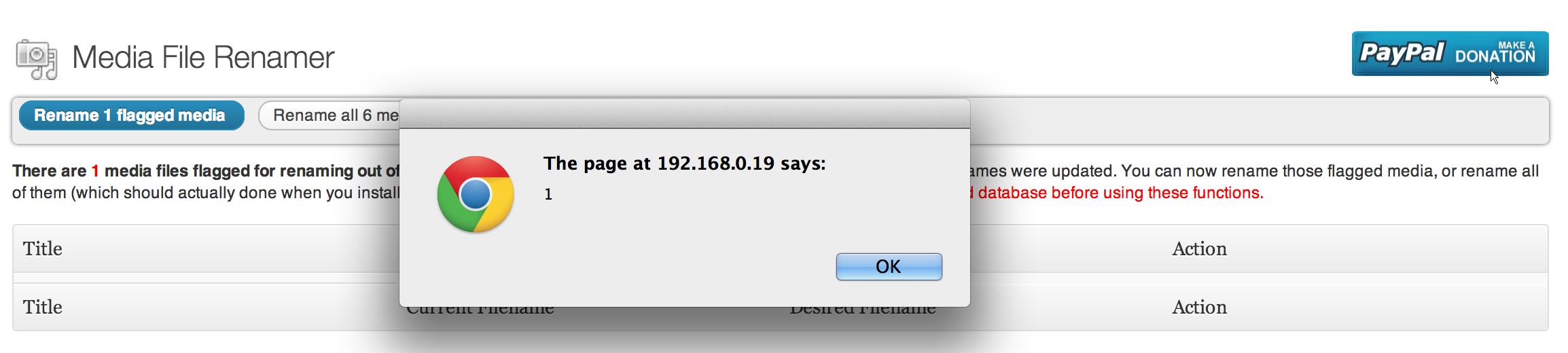
PoC: If a user with permission to add media or edit media uploads a file with "<script>alert(1)</script>" as the title they can XSS the site admin user.